Featured
Table of Contents
- – Vpn Protocols Compared: Which Is The Best?
- – Aws Vpn - Faqs - Amazon Web Services (Aws)
- – What Is Openvpn & How To Use It?
- – Openvpn - Wikipedia
- – What Is Openvpn Protocol And What Are Its 5 H...
- – Vpn Protocols And Connection Types - Ipvanish
- – What Is Openvpn Protocol? - Nordlayer Learn
- – Openvpn Over Tcp Vs. Udp: What Is The Differ...
- – What Is Openvpn Protocol And What Are Its 5 ...
Vpn Protocols Compared: Which Is The Best?
It is possible to utilize Open, VPN freely since it is open source, which means you are free to use it if you follow the conditions in the software application license agreement. While the code is complimentary, it's worth pointing out that it requires a lot of manual setup (i.
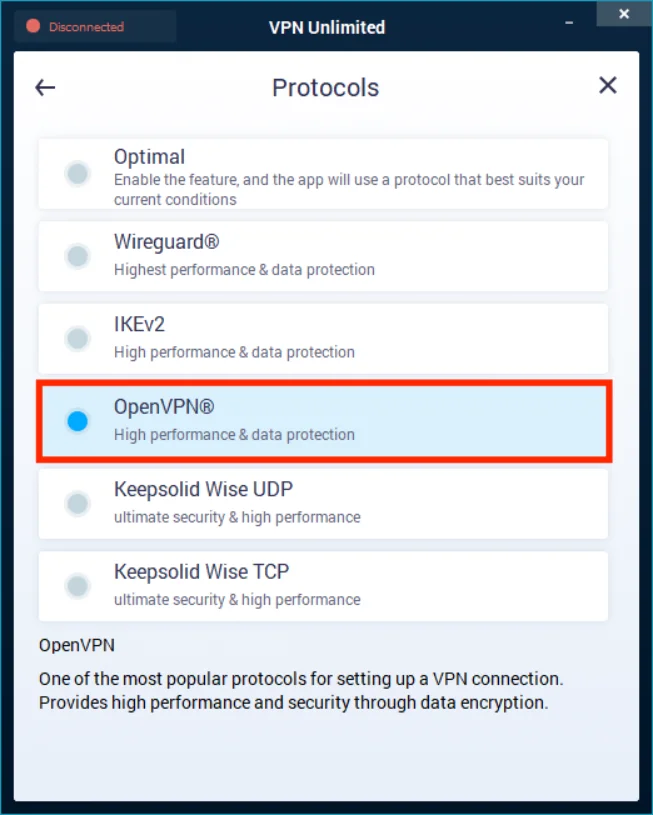
You will benefit from the complimentary, non-proprietary nature of the procedure while paying to utilize it through a productized VPN service like Express, VPN or Nord, VPN. What is it excellent for if it's not super-safe? You might have seen that your VPN breaks this out as two procedures: Open, VPN UDP and Open, VPN TCP.
Aws Vpn - Faqs - Amazon Web Services (Aws)
A key function of Open, VPN is that it is extremely versatile and one variation can differ from another. Your VPN provider might utilize a various version than what's being utilized by another company.
When they find a bug, they repair it and they also keep attempting to include brand-new functions to it. This is the main reason behind the adaptability of Open, VPN.There are a number of ciphers supported by Open, VPN. As a standard, Open, VPN implements 256-bit file encryption, although it's not necessary (you might have seen some VPN providers offering Open, VPN with AES-128 bit file encryption).
What Is Openvpn & How To Use It?
So no matter how your VPN company may choose to establish their servers and connectivity, Open, VPN will appropriate for them. There are some protocols that are device-dependent. For example, PPTP does not work on Mac computers. Open, VPN, on the other hand, can run on Windows, Mac, Android, i, OS, Linux, and other platforms.
Since Avast is a big name in the cybersecurity industry, you would expect they don't keep any logs. Regrettably, they do. This implies while the federal government may not know what you're doing, the VPN company understands when you logged in and when you logged out. And this details can, if needed, be handed over to the government.
Openvpn - Wikipedia
I tested 30+ VPNs and found the best ones that use Open, VPN. It comes with the protocol pre-configured along with its other security procedure choices.
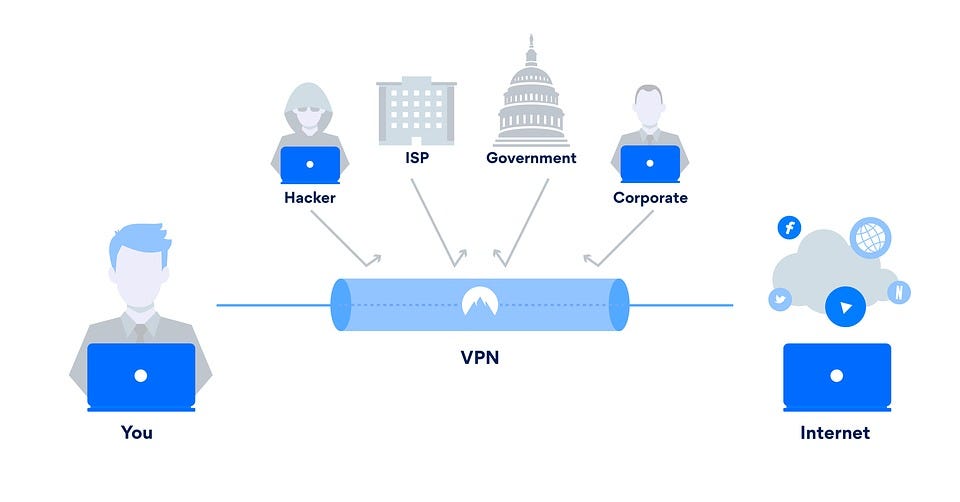
This has actually produced a community of VPN procedure developers and users who continuously test, update, and improve the protocol. Like any VPN, Open, VPN. Different procedures do this in other, unique, and exceptionally complicated manners. Making it so no one can get to your delicate and private details. by covering it in layers of additional information.
What Is Openvpn Protocol And What Are Its 5 Hype ...
Premium VPNs, like Express, VPN, currently have the procedure preconfigured. Unless you are experienced in manual setup, working with Open, VPN can be really lengthy and complex.
The settings can be changed and customized depending on your preference. The same chooses when you utilize Open, VPN by means of a VPN supplier. Open, VPN works in a different way based upon the settings and setups. that continually updates Open, VPN. This neighborhood works to update, improve, and repair the protocol when required, which might change how it runs as updates present.
Vpn Protocols And Connection Types - Ipvanish
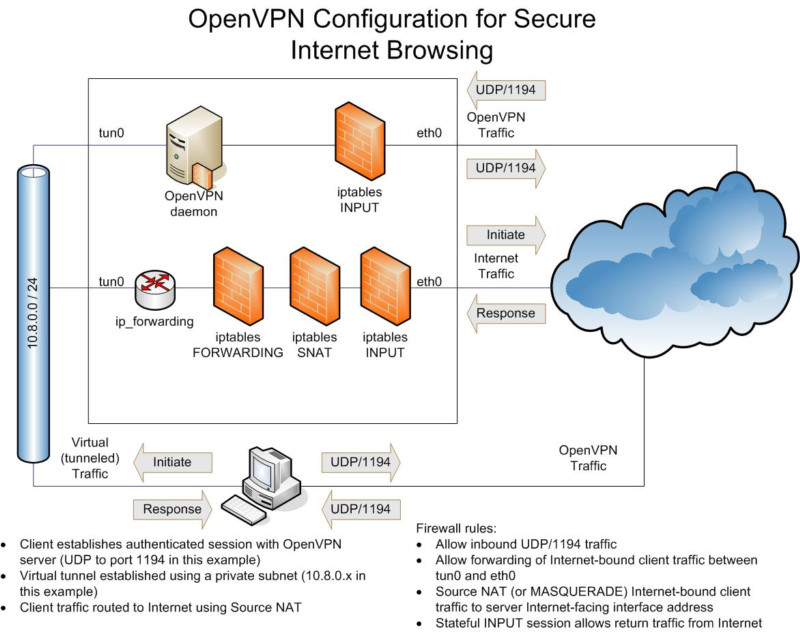
SSL/TLS procedures share the keys to encode and decode details sent between devices. This is where your data is secured. The most typical encryption approaches are Cha, Cha and AES 256-bit encryption. These ciphers utilize secrets the aspects that "unlock" encrypted messages, for example, 256 0s and ones, making them very tough to decipher.

This protocol manages how your information is sent and guarantees everything sends in the correct order, so there's no jumbling of information. It does this by way of a restorative system within the protocol.
What Is Openvpn Protocol? - Nordlayer Learn
VPNs like Cyber, Ghost deal Open, VPN on both Android and i, OS. Utilizing Open, VPN with a VPN can assist you avoid this.
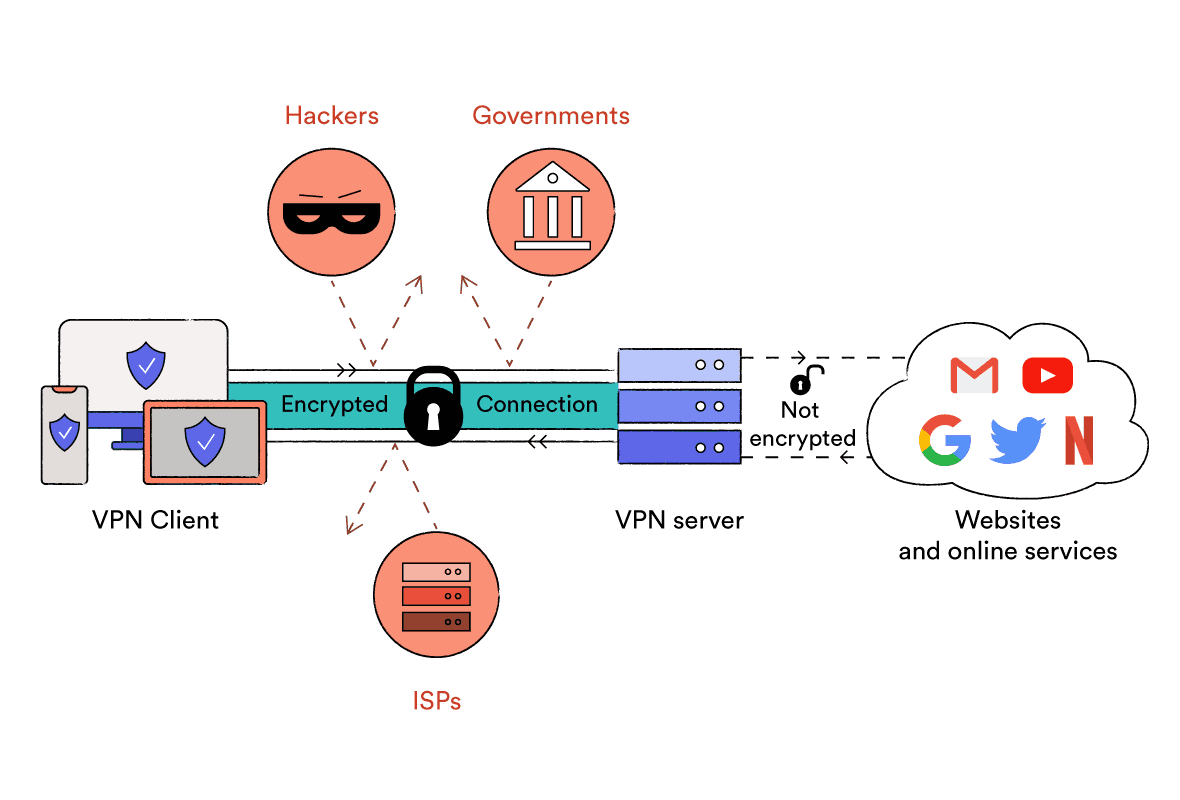
Open, VPN is even generally thought about safe from spying by the NSA (United States National Security Agency), which has advanced methods and a large budget, which is very outstanding. as an open-source procedure, making it more reliable. When a big company manages a protocol, you have to trust it not to share your info with government companies or other companies.
Openvpn Over Tcp Vs. Udp: What Is The Difference?
I suggest using a premier VPN, such as Express, VPN, so you can trust that your information remains personal. I recommend Express, VPN as Open, VPN comes pre-configured, and it won't jeopardize your speed.
Go to settings and choose Open, VPN. Then, choose TCP (more secure) or UDP (better speeds). You can now search the web, play video games, stream videos, and more with confidence that your data is kept personal. Tech-savvy users can do so reasonably quickly, however there is still room for mistake in this procedure, and any errors could be hard to fix.
What Is Openvpn Protocol And What Are Its 5 Hype ...
Your actual place is secured with IP/DNS leak protection. I used ipleak. net to check Express, VPN for leaks and discovered none. It does this by changing the encryption secrets often. So, it would be unreadable even if someone were to get their hands on your information.
Table of Contents
- – Vpn Protocols Compared: Which Is The Best?
- – Aws Vpn - Faqs - Amazon Web Services (Aws)
- – What Is Openvpn & How To Use It?
- – Openvpn - Wikipedia
- – What Is Openvpn Protocol And What Are Its 5 H...
- – Vpn Protocols And Connection Types - Ipvanish
- – What Is Openvpn Protocol? - Nordlayer Learn
- – Openvpn Over Tcp Vs. Udp: What Is The Differ...
- – What Is Openvpn Protocol And What Are Its 5 ...
Latest Posts
9 Best Vpns For Home And Business In 2022
Best Vpn For Business
The Best Vpns For Small And Home-based Businesses
More
Latest Posts
9 Best Vpns For Home And Business In 2022
Best Vpn For Business
The Best Vpns For Small And Home-based Businesses